Multiplexing over https: Difference between revisions
imported>Hendrik Brummermann No edit summary |
imported>Hendrik Brummermann mNo edit summary |
||
| (5 intermediate revisions by the same user not shown) | |||
| Line 16: | Line 16: | ||
[[Category:Marauroa]] |
[[Category:Marauroa]] |
||
{{#breadcrumbs: [[Marauroa]] | [[Navigation for Marauroa Developers|Internals]] | [[Marauroa Roadmap|Roadmap]] | [[Multiplexing over https]] }} |
|||
Latest revision as of 09:06, 20 September 2010
This article describes a future concept. It may still have some open issues and it was not decided, yet, whether to implement it in this way.
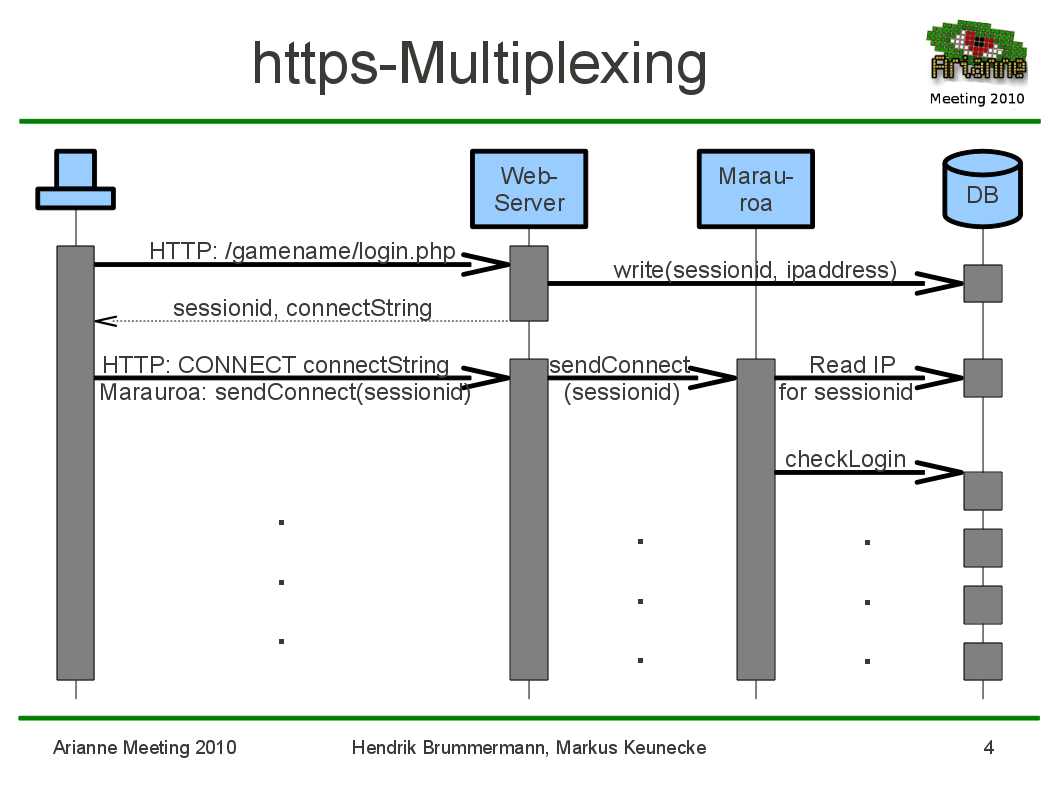
In order to encrypt the complete client server communication and to make the marauroa protocol more firewall friendly, it should possible to tunnel it over https.
There is, however, the issue that we want to be able to use a normal https server serving web content on the same ip-address.
It would be possible to send a CONNECT 127.0.01:32160 http-command but this will cause the game server to see all connections as coming from localhost.
A possible solution would be to request a sessionid with an normal https-GET-request from a php page. This php-program will store the client ip-address and the sessionid in the database. Then the client does the CONNECT-dance and sends that sessionid. If there is no sessionid, the login is rejected. If there is a sessionid, marauroa will use that to lookup the real ip-address and log it in loginEvent
 {{#breadcrumbs: Marauroa | Internals | Roadmap | Multiplexing over https }}
{{#breadcrumbs: Marauroa | Internals | Roadmap | Multiplexing over https }}